As the world becomes increasingly digital, the need for effective cybersecurity measures becomes more important than ever. With the rise of internet usage, online transactions, and connected devices, there is a higher risk of cyber threats such as data breaches, identity theft, and malicious attacks.
Cybersecurity is the act of protecting networks, systems, and programs from digital attacks. It’s a critical part of any organization’s security infrastructure, as it helps protect sensitive data and prevent unauthorized access to systems.
If an organization’s systems are breached, it can lead to the loss of sensitive information, disruption of services, and financial losses. Cybersecurity is also important for individuals, as it helps to protect personal data and financial information from being stolen or misused.
The Importance of Cybersecurity in a Digital World
When it comes to cybersecurity, organizations should take steps to ensure that their networks and systems are secure. This includes using strong passwords, encrypting data, and implementing two-factor authentication. They should also regularly monitor for threats and take steps to mitigate them.
Organizations should train their employees on cybersecurity practices and ensure that their systems are updated regularly with the latest security protocols. This is vital, as taking precautionary actions are essential for their infrastructure’s well-being.
In addition to data and systems, cybersecurity can also help protect the reputation of an organization. A data breach or other type of cyber-attack can cause significant reputational damage, leading to customer distrust, loss of business, and financial forfeiture.
Organizations should take steps to ensure that their networks and systems are secure. By taking the necessary steps to protect their systems and data, organizations can protect their customers and their reputation. They can also keep important data out of the wrong hands.
What is Cybersecurity?
At its most basic level, cybersecurity is the practice of protecting a company or an organization’s networks, devices, and personal data from malicious attacks. It involves identifying potential threats, developing strategies to mitigate those threats, and implementing the appropriate measures to keep data and systems secure.
The internet has become a major part of our lives, and with that comes the need for increased security. Cyber-attacks are becoming increasingly common and sophisticated, and it is important to be prepared for them. It is critical to understand the risks associated with cybersecurity and have a plan in place to protect your organization.
During the last few years, the term cybersecurity has developed a strong level of digital presence within the technology, making it a popular topic. Increasingly, companies are beginning to create new networks to support the bandwidth needs of their employees as remote work becomes the norm in today's day and age. Although this flexible work structure has allowed so many companies and offices to move to a more malleable working structure, it has also led to an increase in cyber-attacks.
Why is Cybersecurity Important?
95% of cybersecurity breaches are caused by human error, according to Cybnit.
There is no doubt that security is one of the most important elements of a digital security strategy for any organization and user. Cybersecurity plays a vital role in preventing attacks that aim to manipulate or destroy an organization's data.
Individuals and organizations often employ cybersecurity to protect computerized data centers that hold valuable information. If tampered with or exposed, an individual or company could be compromised. Common areas targeted by hackers include company wide networks, devices, and anything that can be connected to an internet access point.
Awareness of these threats is incredibly important and involves understanding the different types of cyber threats, the impact they can have, and how they can be mitigated. Browsing the web, exchanging emails and communicating on social media/other websites can put you, your colleagues and even your business in a compromised position if you’re not thinking about cybersecurity.
Cybersecurity awareness is imperative, but it must also be paired with the ability to make the right choice when a potential threat arises. For your business to be adequately protected from cyberattacks, it's essential that all relevant parties receive rigorous and comprehensive training.

The Benefits of Cybersecurity
The importance of cyber security in the digital age cannot be overstated. In today's interconnected world, a single security breach can have far-reaching consequences.
Over 145 million people's personal information was stolen in the 2017 Equifax breach, and over 500 million people's personal information was stolen in the 2018 Marriott breach. These breaks monetarily affected the organizations in question and brought about client trust misfortune. As a result, cybersecurity is necessary to safeguard individuals and businesses from the devastating effects of a security breach.
Services such as Microsoft Defender, Microsoft Secure Score for devices, and Intune actively prevent attacks from ever occurring when implemented into an organization's security posture.
Benefits of implementing and maintaining cybersecurity practices include the following advantages:
- Preventing Data Breaches
- Network Security
- Prevention of Unauthorized User Access
- Endpoint and Device Protection
- Email Threat Security
Check out our complete guide to email security with a top solution comparison!

What is a cyber-attack?
It is important to realize that cyber-attacks are deliberate attempts by external or internal attackers who wish to expose, exploit, or compromise the confidentiality, integrity, and availability of an organization's or individual's information systems. The goal of a cyberattack is to cause damage and disruption to computers, devices, networks, applications, and databases through illegal methods, tools, and approaches.
The following list highlights some of the most common types of cyber-attacks:
-
Malware
-
Ransomware
-
Phishing
-
The brute force method
-
Spamming
How to prevent cyber-attacks?
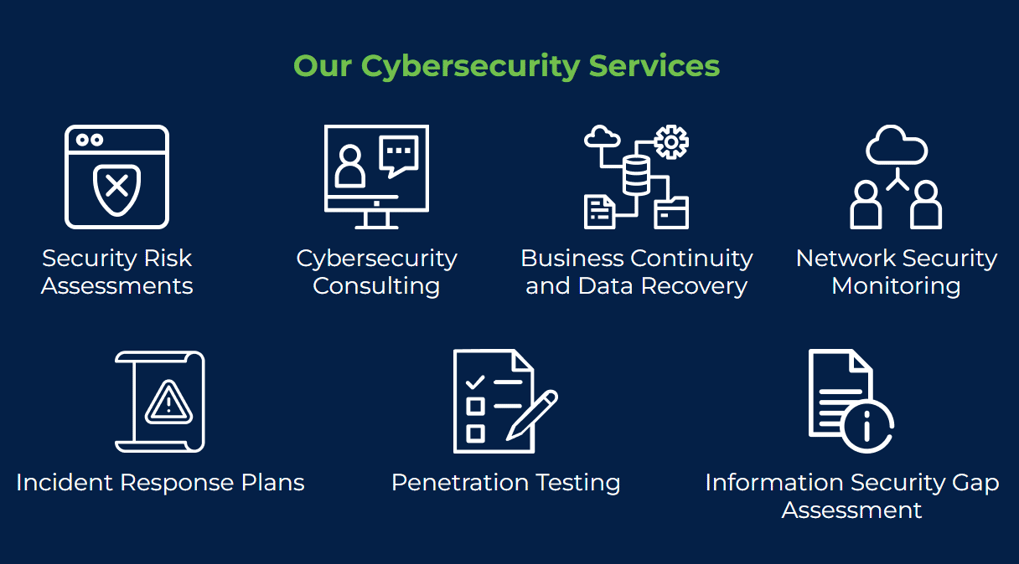
While it is important to identify these attacks, it is not beneficial to your organization unless you have set a plan of action. Datalink Network offers a variety of cybersecurity services made to fit your organization’s unique needs.
As a Microsoft Solutions Partner, we offer various services such as Microsoft Defender for Endpoint. Microsoft Defender is an enterprise-grade protection for end-user devices such as tablets, cell phones, laptops, and more. This holistic, cloud-based endpoint security solution helps to prevent, detect, investigate, and respond to cyberattacks that threaten your endpoints. Because this solution is based in the cloud, there is no additional deployment or infrastructure needed, and it auto-updates, leaving your endpoints protected and updated at all times.
Backed by security experts, Microsoft Defender for Endpoint is built on the deepest threat optics available. In fact, Microsoft employs over 3,500 global security experts to help keep you and your data secured. This deep knowledge in cybersecurity helps Microsoft Defender for Endpoint utilize preventative protection techniques, post-breach detection, automatic investigation and remediation, and more.
An additional service that aids in cybersecurity, more specifically for devices, is Microsoft Intune.
Microsoft Intune is a cloud-based mobile device management (MDM) service that helps organizations manage and secure their mobile devices. Intune provides a comprehensive set of features including device management, application management, information protection, and more. With Intune, organizations can manage both corporate-owned and personally owned devices in a single console.
Microsoft Intune is built on top of the Microsoft Azure platform and uses the same security and compliance controls as Azure. This makes it easy for organizations to integrate Intune with their existing Azure infrastructure. Intune also integrates with other Microsoft products and services such as Office 365, Windows 10, and Enterprise Mobility + Security (EMS).
Microsoft Intune Features:
- Manage and secure your mobile devices from anywhere.
- Set up and manage device policies and compliance policies.
- Deploy apps to your devices.
- View real-time reports on device status and activity.
- Lock or wipe a lost or stolen device remotely.

Five Tips to Follow to Protect Your Devices
While cybersecurity services can be important safety valves in an organization's infrastructure, there are many basic practices that can also be added into your day-to-day work to ensure that the risk of data breaches can be minimized.
Here are a few simple ways that can help minimize threats to your company and its personal data:
1. Develop a cyber security awareness training process
A strong cyber security strategy would not be successful if the employees are not properly educated on company policies and incidence reporting. Even the best technical defenses may fall apart when employees make unintentional or intentional malicious actions, resulting in a costly security breach. Educating employees and raising awareness of company policies and security best practices through seminars, classes, and online courses is the best way to reduce negligence and the potential of a security violation.
Identifying all valuable assets and prioritizing them based on the impact caused by their compromise should be part of an organization's formal risk assessment. Organizations can then decide how best to allocate their resources for securing each asset.
3. Implement policies and procedures that ensure password security
They should also be updated regularly to help protect against compromised passwords. Industry standards recommend strong passwords and should be enforced by organizations. Furthermore, password storage should follow industry best practices and strong hashing algorithms.
4. Safely browse the internet
Whenever possible, stay away from sites offering potentially illicit content. On many of these sites, malware is installed on the fly or malware can be downloaded. Using a modern browser, such as Microsoft Edge, will protect your computer from malicious code.
5. Review security on a periodic basis
Source code reviews, architecture design reviews, and application penetration testing are all often included in routine security reviews and should be considered when an organization is looking to identify security vulnerabilities and mitigate them promptly. This should be of the highest priority in an organization's cybersecurity plan.
What is security posture?
An organization's security posture is its overall security status. This is based on the software, network, services, and other aspects of an organization's security. In order to make informed decisions regarding your cybersecurity plan, you need to understand your organization's strengths and weaknesses.
By regularly checking your security posture and patching holes as needed, you are more likely to remain secure from cybercriminals looking for easy access to your network.
So, how do you determine your security posture? Datalink Networks offers a Free Network Security Assessment, which identifies vulnerabilities in your environment and provides you with a security report card to increase security and lower risk.
Additionally, you can schedule routine penetration testing. This is a form of ethical hacking which identifies security gaps and an organization’s ability to respond to threats. By performing a pen test on your organization’s network, you review the hacking process cybercriminals use to gain access - so you can ensure that all avenues become dead ends.
Conclusion
While there are many threats in the world of cybersecurity, it is essential to know that there are ways in which they can be counteracted. From advanced steps, such as implementing Microsoft Defender into your cybersecurity plan to simply including complex passwords to your network’s log ins, the fight against cyber-attacks is not impossible.
Need help identifying your organization's security gaps to help prevent cybersecurity breaches in your organization?





